News
05.03.20 Released Captain H00K: a free keylogger and hooker. Captainhook is a free and lightweight keyboard and mouse keylogger and hooker; rules can be provided as arg or as file, small size, can be easily injected in memory for filelessness
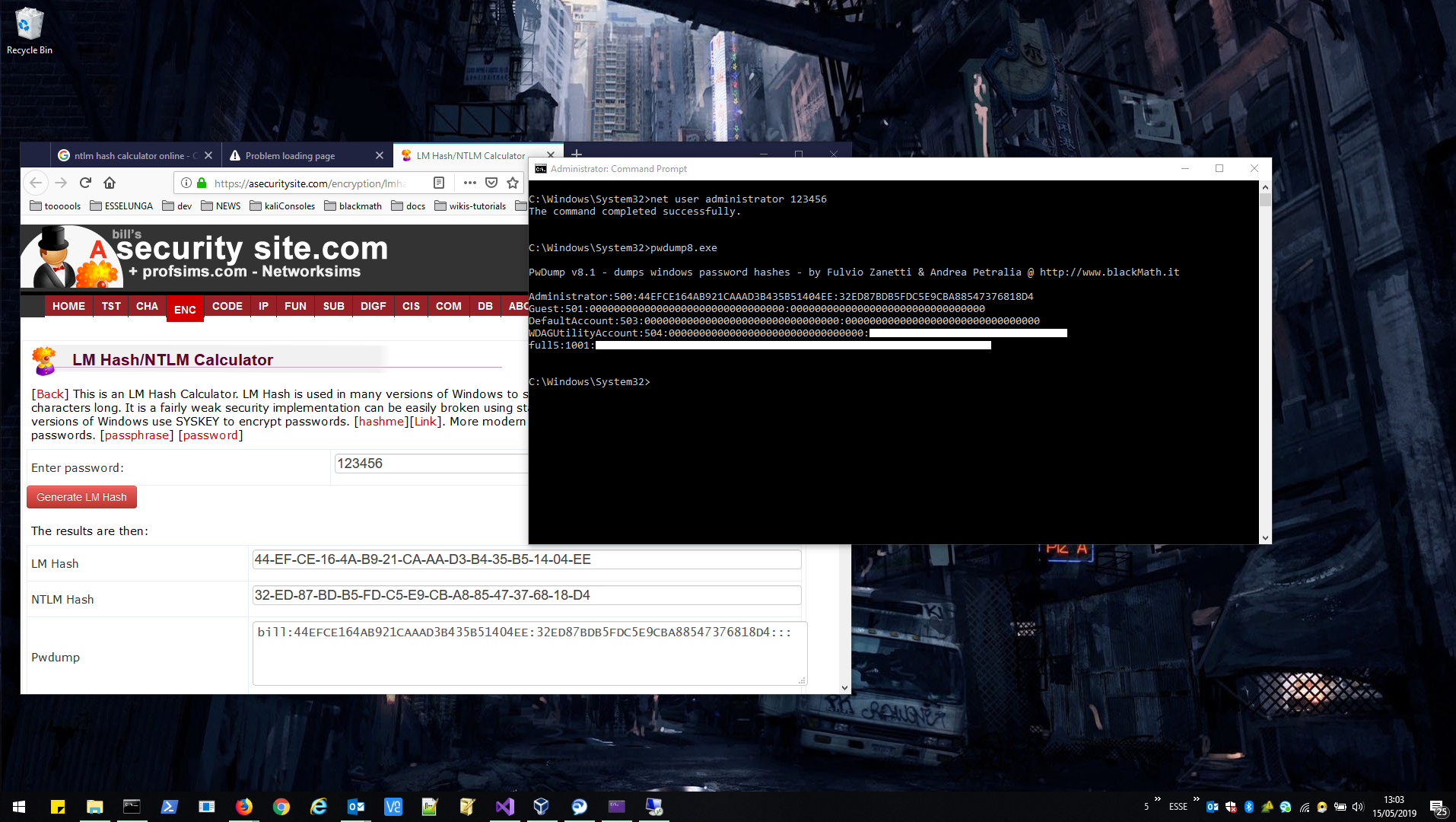
25.06.19 Released pwdump - version 8.2
• Added support for domain cached account
• Fully supporting dump from file (both SAM and SECURITY reg hives)
• Minor bugfix
11.05.19 Released a new version of pwdump: pwdump8 by blackmath now supports AES-128 encrypted hashes and works on Windows 10 v1607 and later As no source code is available since pwdump version 6, we've rebuilt it all from scratch. Please submit any bug / suggestion to info@blackMath.net, source code will be available soon.. enjoy your(..or not..) hashes!!
07.06.17 We are on Twitter
25.05.17 Released a porting of the Infamous Esteemaudit RDP exploit on GitHub
08.05.17 Released Shiva 1.0 source code on GitHub
• Shiva is a C# Ransomware for Windows platform.
23.03.17 We are on GitHub
• We opened a new profile GitHub to release minor code projects, exploits and other stuff...
21.07.16 Released Darkexec ver 1.3
• New token output provides Domain\Username, Session, Impersonation Level, Process ID, Thred ID
• No more windows displayed in loopback connections
• Fixed setting ACL in Interactive mode
• Asks session number if is not passed by
• Improved dynamic-lenght buffer for output
• Improved Token search engine performance
• Improved more detailed Error Handling
• Now working on "WORKGROUP" machines too
• Bug fixes
Projects
• PWDUMP 8
We decided to add a new version in the pwdump saga just because since win 10 v1607 was released, MS moves obfuscation techniques away from RC4 encryption to AES (128 cbc-mode) so, on those systems, tools like pwdump7 and others no more dumps the nt\lm hashes correctly. Pwdump8 requires administrative privileges, as previous releases; binaries can be found in the download section, source code will be available on GitHub asap.
- Compatible with AES-encrypted hashes
- Supported windows versions: 2000/XP/Vista/7/2008/8/8.1/10/2012/2016/2019
- Works with local system, and dumped registry files
• ESTEEMAUDIT-METASPLOIT
We released a porting for Metasploit of the infamous Esteemaudit RDP Exploit leaked from Equationgroup (NSA).
Vulnerable machines are:
- XPSP0 Windows XP SP0
- XPSP1 Windows XP SP1
- XPSP0|1 Windows XP SP0 or SP1
- XPSP2 Windows XP SP2
- XPSP3 Windows XP SP3
- XPSP2|3 Windows XP SP2 or SP3
- W2K3SP0 Windows 2003 SP0
- W2K3SP1 Windows 2003 SP1
- W2K3SP2 Windows 2003 SP2
- W2K3SP1|2 Windows 2003 SP1 or SP2
Source code and ruby file on GitHub
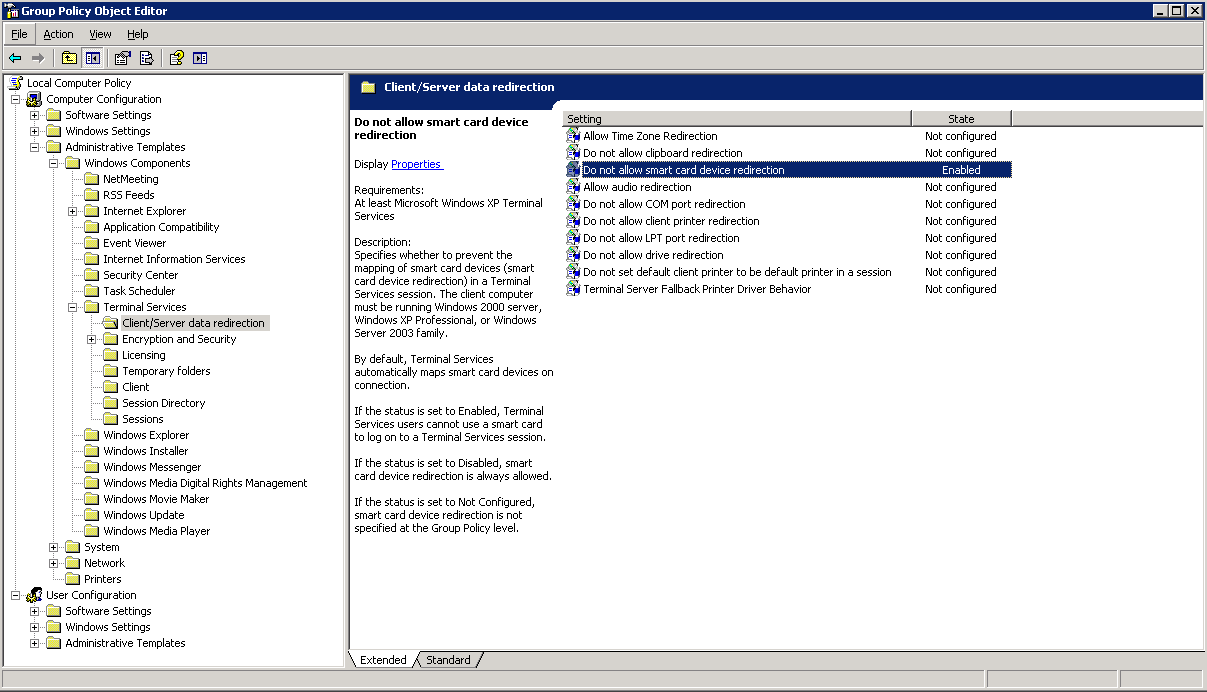
HOW TO MITIGATE ON WINDOWS SERVER 2003:
- Run gpedit.msc
- Go to Computer Configuration\Administrative Templates\Windows Components\Terminal Services\Client/Server data redirection\
- Set enable on "Do not allow Smart Card device redirection"
- Restart the server.
Same can be done on a DC via GPO.
• SHIVA
C# Ransomware for Windows platform
Shiva was born after our recently study about Ransomware and to demonstrate how simple is to code one. We are going day by day to learn more about this kind of threat and we belive that it's really important to show you how they are builts to lern to mitigate them.
- Uses AES algorithm to encrypt files.
- Encrypt local, network and external disks.
- Use random extensions for encrypted files.
- Sends encryption key to a server.
- Delete encryption key from memory.
- Encrypted files can be decrypted in decrypter program with encryption key.
- Creates a Html file with given message.
- Autodelete itself at the end of execution.
- Small file size (210 KB)
• Captain HOOK
a free mouse and keyboard keylogger, proxy and hooker

This program is a keyboard and mouse hooker, rule file can be filled with keycodes to block, one per line as in example "rules.txt" file and max 256 entries (standard keyb are 110 keys or less..). It can also be used as a keylogger, just run the program without rules for keylogger only mode. Keycodes can also be provided as additional arguments into command line if -f is omitted and -k (keyb block mode) is present.
Small file size (600 KB), it can be easily injected into memory.
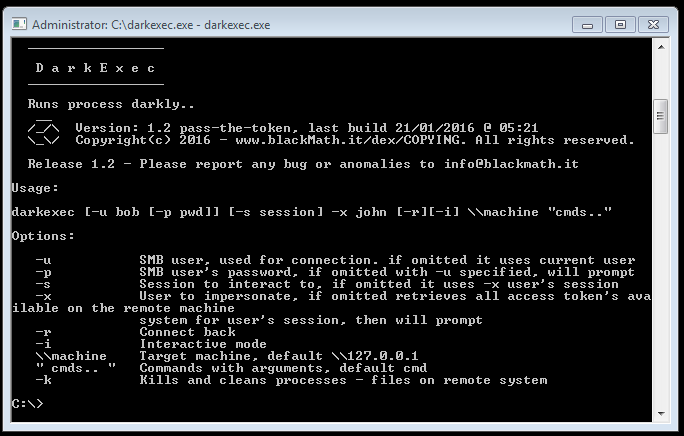
• DARKEXEC
Access Token manipulation, a new way to surf 'n a domain.
1. The scenario
------------------
A typical scenario is a Windows context and generally a Domain.
Which are the reasons to obtain explicit user's credentials when you already have got some system access to a workstation ?
1. Maintaining access.
2. Gain access to user's environment contents.
3. Take control on the remote user's resources.
Considering that obtain credentials just for access-manteining is stupid, dangerous, logged.
Such disadvantages are exposed using different techniques to obtain access as pass-the-hash or pass-the-ticket ?
1. If handled separate and manually they are not transversal, and hard to use with the different communications protocols.
2. Hard to automate if compared to tools like the famous SMBEXEC.
In this kind of scenario, having access to a machine with administrative privileges, having at least another user's process started, it is possible to gain full access to its security context according to some technique, we can call it pass-the-token.
In the same condition mentioned above, Darkexec, manipulating Users Access Token in all differents Winsta, is a tool made to bypass the Microsoft Windows OS's user-context security boundaries, implemented from win7 to win10, until now (server editions included).
2. Access Token
--------------------
An "access token" is an object that describes the security context of a process or thread. The information in a token includes the identity and privileges of the user account associated with the process or thread. When a user logs on, the system verfies the user's password by comparing it with information stored in a security database. If the password authenticated, the system produces an access token. Every process executed on behalf of this user has a copy of this access token.
The system uses an access token to identify the user when a thread interacts with a securable object or tries to perform a system task that requires privileges.
Access tokens contain the following information:
• The security identifier (SID) for the user's account
• SIDs for the groups of wich the user is a member
• A logon SID that idenfies the current logon session
• A list of the privileges held by either the user or the user's groups
• An owner SID
• The Sid for the primary group
• The default DACL that the system uses when the user creates a secureable object without specifying a security descriptor
• The source of the access token
• Whether the token is a primary or impersonation token
• An optional list of restricting SIDs
• Current impersonation levels
• Other statistics
For all the list of functions to manipulate access token please follow the link below
[view references at : https://msdn.microsoft.com/en-us/library/windows...]
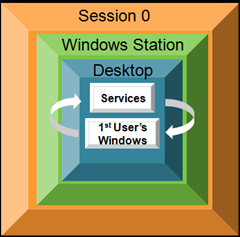
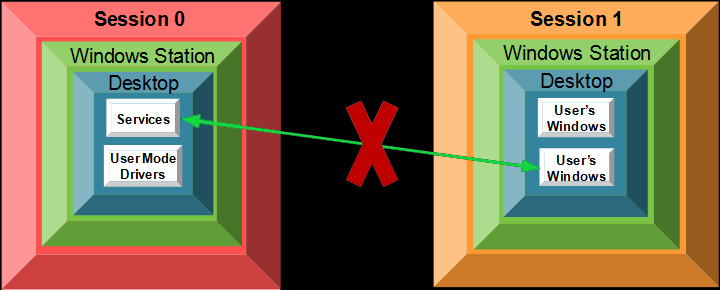
2. Windows Stations user's session architecture
--------------------------------------------------------
The diagrams below show the relationships between sessions, windows stations, desktops and services in Windows Vista as compared to earlier operating systems
[view references at : http://blogs.technet.com/b/askperf/archive/2007...]
This is a classic workstation scheme, having only sessions 0 and 1, 0 for service session and 1 for the unique available user attached to the console. In a terminal server we will have the same layout, just sessions numbers normally start form 2, and there are more than one user logged on..
The user session contains a "Windows Station" (WinSTA) that host by itself 3 (by default) or more desktop (Ex. CTRL+ALC+CANC, Screensaver, user desktop)
for these three objects the sessions 2 and 3 are mutually inaccessible and separate each-others but the service session 0 can interact with both.
N.B. when we talk about "separate", we don't mean "physically", in memory, but only like referenced to the classics callings used by winAPI to make user-token-manipulation.
In fact, the first time everything was carried out writing a kernel mode driver program, editing users token directly, in memory, with the same positive result.. anyway existing system libraries for do that was quite useless and dangerous to use a kernel mode approach.. (Exception made to different situations where a GPO bypass may be required... and we are working on it... ;) )
The following link explain shortly how to apply the basics concepts of a Securable Object to a WinSta or Desktop Objects and why we are talking about:
https://msdn.microsoft.com/it-it/library/windows/desktop/ms687391%28v=vs...
http://mscerts.wmlcloud.com/windows//Windows...
so windows code isn't public, but you can search and find a lot more about this.. briefly: user mode and GDI32 processes aren't secureable objects, so windows needs to introduce objects like windows stations, desktops and sessions, that are secureable objects instead, as kernell mode processes are, too.
On this layout, SYSTEM calls different functions to modify and duplicate users token, creating processes in the right security context, with relative privileges.
Abusing system functions, an user granted as Administrator can call SYSTEM for code execution, then it can edit user's token to obtain full and redistributable access "acting" in a different security context.
3. develop, practical exploitation
----------------------------------------
The project is composed by a main distributed executable: darkexec.exe.
The application made a SMB connection to the target, if it’s different from localhost, copying the service executable: dexsvc.
The last runs as a service and, if “connectback” was specified, the client will also start the communication with the named-pipe service.
The service acts and communicate as described:
not interactive mode, it only calls dexsvc.exe in service mode:
1. enables SE_TCB_PRIVILEGE to the calling process.
2. identifies best Access Token from process and threads owned by the users to impersonate - opens processes handle and tokens handle - OpenProcess(), OpenProcessToken().
3. duplicate user token x - DuplicateToken().
4. in connectback execution redirect the input output handles to the calling user PROCESSINFO.
5. modify token’s session if it’s necessary - SetTokenInformation().
6. it “passes” the modified token for execution - CreateProcessAsUser().
interactive mode, make two call to dexsvc.exe: as service and as executable too:
1. gets the commands from the local dexsvc, which holds the pipe for communication
2. identifies best Access Token from process and threads owned by the users to impersonate - opens processes handle and tokens handle OpenProcess(), OpenProcessToken()
3. duplicate user token x - DuplicateToken().
4. in connectback execution redirect the input output handles to the calling user PROCESSINFO.
5. modify token’s session if it’s necessary - SetTokenInformation().
6. modify the ACL for WinSta object and Desktop, it makes an interactive viewable windows graphically correct (no matter psexec!! ^_^ )
7. it “passes” the modified token for execution - CreateProcessAsUser().
Practical demonstration
4. conclusions
-----------------
Thanks to the Msdn world, Microsoft itself, others people and stuff... :)
We are working a lot to make it better and implement new interesting features, so if you want to help us please report any bugs, anomaly or everything else to info@blackmath.net
Thank you all, Enjoy !!!
Download
![]() PwDump8 - dump window's hashes - 32bit | Windows
PwDump8 - dump window's hashes - 32bit | Windows
![]() Darkexec - ver. 1.3, #pass-the-token - 32bit | Windows.
Darkexec - ver. 1.3, #pass-the-token - 32bit | Windows.
Shiva - Source code for 32bit-64bit | Windows.
![]() CaptainH00k Keylogger and Hooker - 32bit | Windows.
CaptainH00k Keylogger and Hooker - 32bit | Windows.
© 2015 - Copyright Blackmath.net, all rights reserved.
